The healthcare industry receives 2 to 3 times more cyber-attacks than the financial services sector where there is malicious use and demand for high value, sensitive patient data.
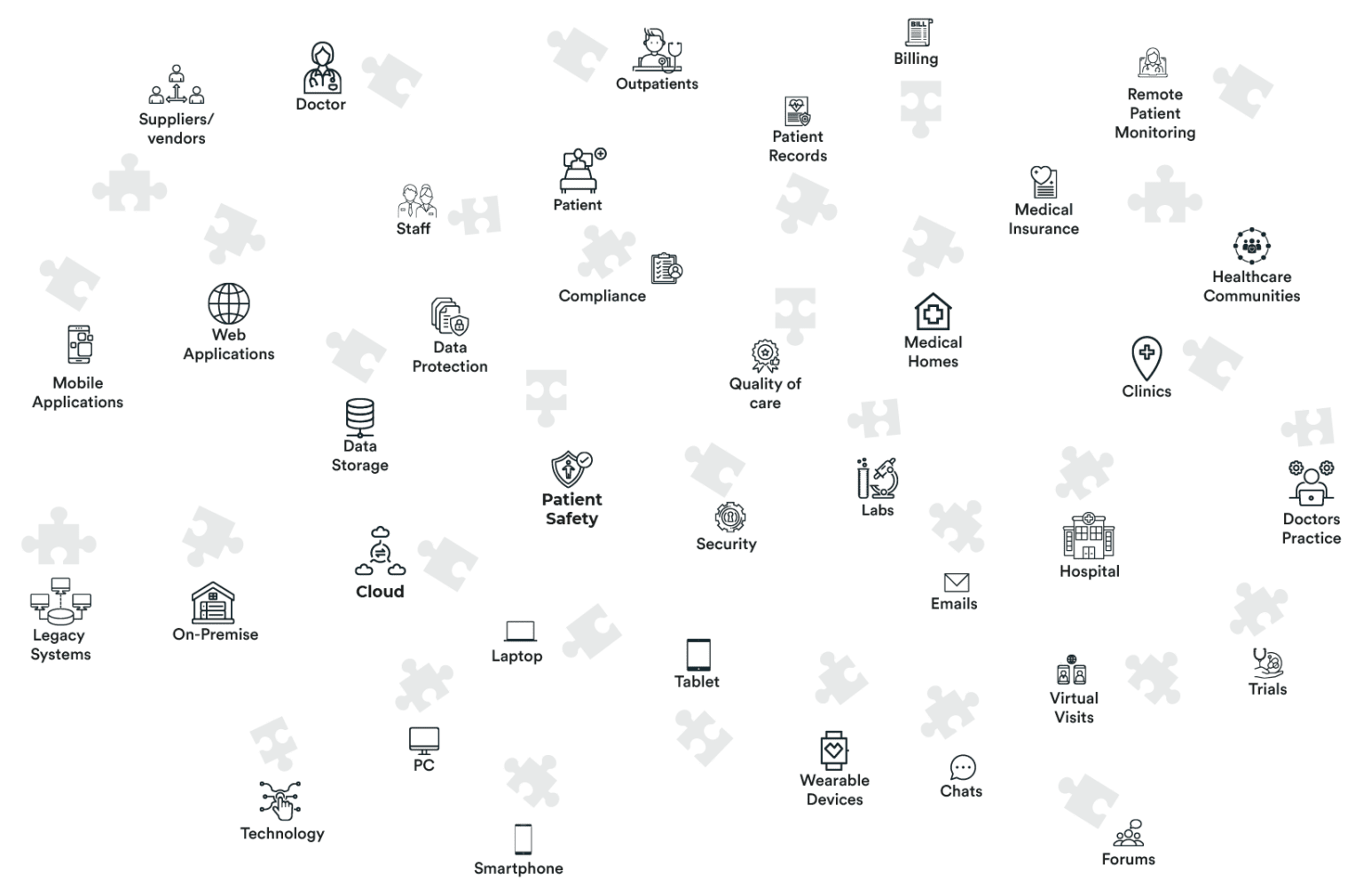
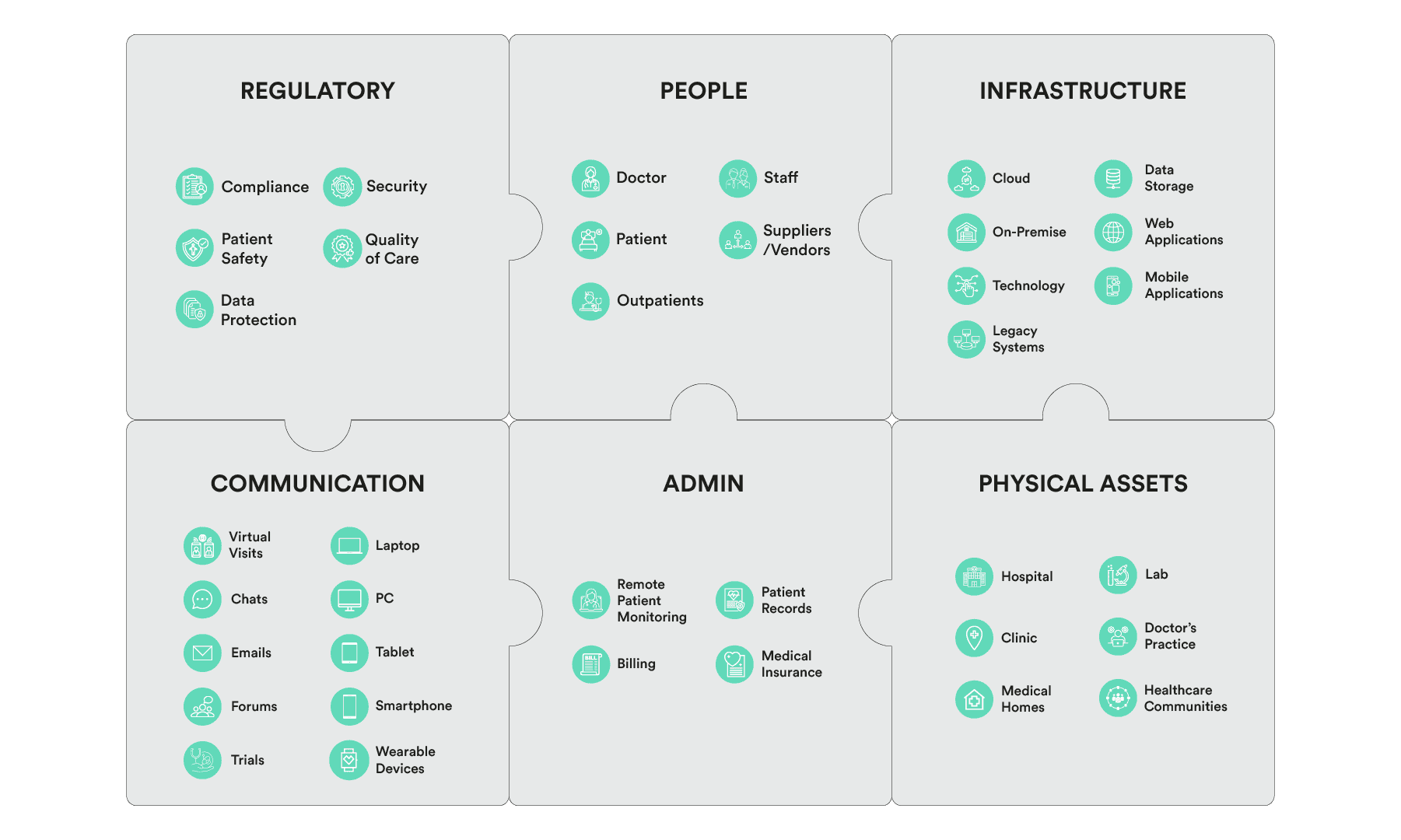
The complexity of a distributed asset environment and fragmented or siloed technologies (including IoT and SCADA) further exasperates the problem.
Security Vulnerabilities
Unsecured medical devices and equipment running through IoT/ IoMT, SCADA, etc can result in the compromise of sensitive patient information, leading to identity theft, fraud, and legal repercussions.
Complexity of IT Infrastructure
Healthcare systems often involve a complex ecosystem of medical devices, electronic health records, and various IT systems. Inefficient management of digital assets can lead to vulnerabilities.
Data Protection
With a dispersed and non-centralised asset digital infrastructure, the management and control of data becomes a nightmare to stay on top of.
Compliance Challenges
Healthcare providers must adhere to strict regulatory frameworks like GMA (General Medical Association) or HIPAA (Health Insurance Portability and Accountability Act). Failure to comply can result in penalties and damage to the organisation’s reputation.
Sophisticated Cyber Threat Landscape
Cybercriminals are continuously evolving their tactics, making it crucial for healthcare organisations to stay ahead of emerging threats such as ransomware and insider threats.
The BlockAPT Platform enables healthcare organisations to strengthen their cybersecurity defences, ensure the highest standards of data protection and patient trust, streamline security operations, and achieve regulatory compliance.
Centralised Management and Control
With real-time monitoring of healthcare assets offering centralised management with unified visibility, the BlockAPT Platform can connect to every data system and digital asset, allowing for early detection and response to potential security incidents.
Quantum Secure Data Protection
Deploy next-gen communication & asset protection for medical data in motion, or data at rest utilising the award winning MTE® (MicroToken Exchange) technology, ensuring an end to unauthorised access, enhancing data confidentiality and integrity.
Access Control and User Authentication
With the BlockAPT Platform’s role based access control settings, organisations can facilitate a granular level of access control and identity management ensuring only authorised individuals have appropriate access to resources and sensitive data.
Unified Visibility
The unified view across digital ecosystems provides intuitive intelligence and analytics into network activity, system logs, user access, and other crucial security metrics across healthcare entities.
Automated Workflows
Leverage the automation of routine administrative IT tasks and reduce time spent by IT teams suffering from security alerts with advanced prioritisation and remedial actions.
Centralised Management and Control
Centralised management eliminates the need for managing a wide distributed asset management ecosystem within healthcare. Real-time monitoring of data enables proactive threat detection and response, It helps to streamline IT operations, reduce administrative overheads, and improve operational efficiency.
Data Protection and Privacy
BlockAPT Platform’s quantum secure communication capability ensures the confidentiality, integrity, and availability of medical data, protecting patients’ sensitive information from unauthorised access and data breaches.
Federated Visibility and Reporting
A single pane of glass view helps increase holistic network visibility across different ecosystems and provides intuitive intelligence and analytics in one interface.
Enhanced Patient Trust
By prioritising the security and privacy of medical data, healthcare organisations can build and maintain patient trust as well as protect their reputation.
Cost Savings
Through operational efficiencies, better resource utilisation, optimising healthcare network and operational technologies, organisations can achieve greater cost-effectiveness and economies of scale in their security operations.